USA steps up fight against money laundering and nuclear proliferation. It seems North Korean hackers have unleashed a ‘dazzling’ new strain of malware ominously dubbed “Durian” to wreak havoc on South Korean crypto firms. Judge Timothy Kelly from the US District Court for the District of Columbia has ordered the arrest of 279 crypto accounts linked to North Korean operatives.
Confrontation with North Korea on the Cyber Front
This decision comes hot on the heels of a series of US maneuvers aimed at dismantling financial networks facilitating North Korea’s illicit activities. The story, launched by the US government in August 2020, targeted individuals tied to North Korea funneling stolen cryptocurrency onto exchanges and unhosted wallets outside the USA.
These elaborate operations cloak the origins of stolen funds and morph them into hard cash, aiding North Korea in skirting sanctions.
In response, Washington has tightened its controls by sanctioning crypto-mixers – services that make tracking the source of stolen funds a real headache. However, North Korean cybercriminal syndicates deftly sidestep both US and international sanctions by coming up with new money laundering schemes.
How did the Attack Go Down?
According to the threat report from cybersecurity company Kaspersky, the North Korean hacking squad, Kimsuky, has unleashed their latest masterpiece of malware mayhem, the Durian, in a targeted onslaught against at least two cryptocurrency companies.
This was executed through a “persistent” attack, utilizing legit defensive software exclusively wielded by crypto firms in South Korea.
The previously unknown malware, Durian, acts like an installer, serving up a steady stream of malicious software goodies, including a backdoor delightfully named “AppleSeed,” a bespoke proxy tool known as LazyLoad, and other legit tools like Chrome Remote Desktop.
“Durian boasts a full suite of backdoor functionalities, allowing for executed commands, additional file downloads, and their sneaky exfiltration,” as per Kaspersky.
These antics are all part of a grander cyber caper aimed at fleecing cryptocurrency exchanges. Take, for instance, one heist that netted nearly $250 million after an unsuspecting employee clicked on some malware. This malware granted miscreants remote access for some VIP asset management.
“First off, with Durian, the North Korean hackers dished out an extra side of malware called ‘AppleSeed,’ an HTTP-based backdoor usually favored by the Kimsuky crew. Additionally, they employed legit tools, including ngrok and Chrome Remote Desktop, as well as their own proxy tool to access the target machines. Ultimately, the attacker injected malware to pilfer browser-stored data, including cookies and login credentials,” explained Kaspersky.
Lazarus, Kimsuky, and North Korea’s Links
Furthermore, Kaspersky noted that LazyLoad was also used by Andariel, a subunit within the North Korean hacker conglomerate, the Lazarus Group, hinting at a “slight” connection between Kimsuky and the more renowned hacking gang.
First emerging in 2009, Lazarus has made a name for itself as one of the primo crypto hackers’ clubs.
On April 29, independent blockchain sleuth ZachXBT reported that the Lazarus crew had successfully laundered over $200 million in illicit cryptocurrencies between 2020 and 2023.
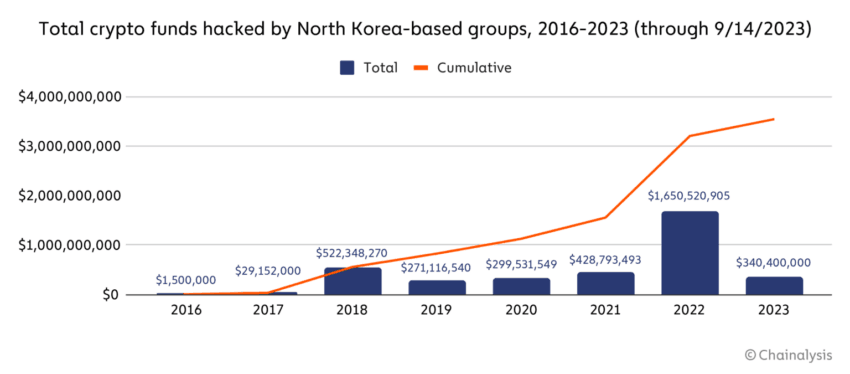
Lazarus stands accused of snatching up crypto goodies worth over $3 billion over the six years leading up to 2023.
They’re credited with pocketing more than 17% — just over $309 million — of the total stolen loot in 2023 alone. According to an Immunefi report from December 28, cryptocurrency losses due to hacks and exploits hit over $1.8 billion in 2023. These funds significantly bolster Pyongyang’s arms programs, including its efforts in nuclear and missile mischief.
More Info:
- Coinbase’s Base Expansion, Nvidia’s AI Reign’s End, Hacker’s $63M Return & Near Protocol’s Chain Signatures
- The Vacation in Montenegro Is Over: Ex-CFO Terraform Labs Extradited To South Korea
According to a group of UN experts, this funding is important as it makes up nearly half of North Korea’s currency inflow. The stakes are high: billions of dollars in cryptocurrency are at risk of being stolen to support Pyongyang’s weapons programs. Continued vigilance is required from the United States and other countries to protect financial systems and prevent the spread of weapons of mass destruction.
Disclaimer: All materials on this site are for informational purposes only. None of the material should be interpreted as investment advice. Please note that despite the nature of much of the material created and hosted on this website, HODL FM is not a financial reference resource and the opinions of authors and other contributors are their own and should not be taken as financial advice. If you require advice of this sort, HODL FM strongly recommends contacting a qualified industry professional.



